Kryha - The manual
The Kryha Home Page
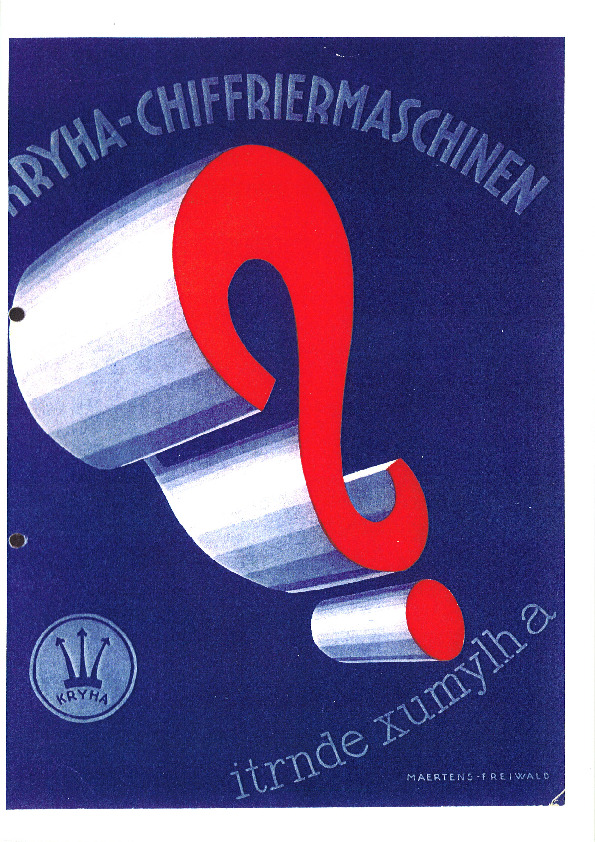
- Iconography
- History
- Working
- Procedures
- The manual. This page.
- Spanish procedure
- My Simulator
- Paper emulator
- Cryptanalysis
- Kryha and CX-52
- Challenges
Introduction
A manual was supplied with every Kryha machine. It was accompanied by a brochure extolling the machine's invulnerability, written by the mathematician Georg Hamel.
This manual, as well as the standard Kryha, dates from at the earliest 1926 (this year is present in the manual) and at the latest 1929.
This website presents two versions of the official Kryha manual:
Note: I am extremely grateful to Klaus Schmeh for providing me with this Kryha manual. It is a very important document for gaining a good understanding of this machine.
There is another version of the Kryha manual, directly in English and entitled "Marconi Standard Model portable KRYHA Ciphering Deciphering Machine". This document is available on the University of Kassel website (see References).
Manual Outline and Summary
-
I. Purpose (p3).
What is the Kryha machine used for? -
II. General (p3).
Provides general information about the machine (dimensions, weight, etc.) - III. Brief explanation of the mechanical process (p3).
-
IV. The Undecipherability of the Machine (p4).
The manual refers to the work of Dr. Georg Hamel, who (supposedly) proves the machine's inviolability. -
V. The machine's potential uses (p5).
The Kryha is intended to be used by diplomats, the military, and companies such as banks. The Kryha (like all encryption machines) is a superior replacement for codes. It ensures secure payments and authenticates transactions. -
VI. Detailed explanation of keying options (p7).
The components of the key are described: the initial position of the wheel, the initial position of the cipher disc, the order of the alphabet of the cipher disc itself, the order of the plaintext alphabet, and the wheel used. The possibility of inserting spaces to vary the encryption is also indicated. -
VII. Ciphering Code Texts (p. 9).
Encryption and ciphertext units have a dual appearance. Each unit contains a letter of the alphabet as well as a number or symbol. Numbers can be used to further encrypt a code. -
VIII. Detailed Instructions for Use (p. 10).
The use of the machine is detailed (how to open it, wind the spring, activate the wheel's advance, etc.). Encryption and decryption are also described. The chapter concludes with an example of a key table.
Notes on the Manual
It should be noted that, unlike the Enigma, the official Kryha manual includes both a description of how the Kryha works and procedures related to securing transmissions. In the case of the Enigma, there are two manuals: one describes the machine's operation (how to change the rotors, etc.), and another describes the procedures for using it within a transmission network (example of a key table, message headers, etc.).
Compared to other cipher machine manuals, the lack of information related to machine maintenance is noticeable: lubrication points, how to disassemble the machine for repair, etc. Similarly, the manual does not offer any measures in case the current key is compromised.
When reading this manual, one gets the impression that its primary purpose is to proclaim the merits of having purchased this marvelous machine: it is very secure, it is easy to use, and the key can be changed indefinitely...
The manual emphasizes the possibilities for changing the key:
- The choice of the encoder wheel (it is advisable to have several)
- The initial position of the encoder wheel.
- The initial position of the internal alphabet relative to the
external alphabet.
A pair of letters, for example A=F, is sufficient to specify this position: the letter A belonging to the internal alphabet, the letter F, opposite the letter A, belonging to the external alphabet. - The orders of letters of the cipher disc (the inner alphabet).
It is even advisable to have several discs to quickly change the encrypted alphabet. - The orders of letters of the plaintext disc (the outer alphabet).
It is even advisable to have several discs to quickly change the plaintext alphabet.
He advises locking the physical components of the key in a safe: the internal alphabet (a wheel), the external alphabet (an arc of a circle), and the coding wheel. The rest of the machine can remain unattended.
My main criticism of this manual, from the perspective of encryption security, is that the "home position" (the initial position of the coding wheel and the initial position of the internal alphabet) is presented as part of the global key. Thus, if a station sends different messages to the same recipient, the home position will be reused, and therefore, the different messages will be in-depth. Their decryption will be possible (see the in-depth page) even without knowing the workings or the key of the Kryha. This lack of knowledge indicates that Von Kryha, his team and his advisors are not experts in cryptology.
Conversely, the document describing the procedures for using Kryha by Spanish nationalists specifies that each message must have a different message key, equivalent to the "home key" in the Kryha manual. This technique prevents messages from being encrypted in depth.
Reference
Web sites
- University of Kassel, Germany [UNIKASSEL VERSITAS] - "Marconi Standard Model portable KRYHA Ciphering Deciphering Machine" [link]