French Army C-36: The start of the war
( )
(
)
( )
)
C-36 Home Page
4.1 Historical background
After Germany commenced the invasion of Poland, France and England (Poland allies) declared war on Germany on September 3, 1939. If we put aside the Norwegian campaign, however, each camp remains quietly behind its own defenses: France and England behind the Maginot Line and the Germans behind the Siegfried Line. During this "calm" period (the Phony War, the "drôle de guerre" in French), rearmament accelerates.
The German offensive began on May 10, 1940. After a succession of retreats by the British, French, and Belgian armies, the Germans conquered the north of France. Pétain's government accepted defeat on June 22 and signed an armistice with the Germans. The British Army, which took refuge near Dunkirk, managed to escape to return to England thanks to an improvised armada (Operation Dynamo).
4.2 French encryption – The late entry into service of the C-36
4.2.1 The beginning of the war – The C-36 is absent
At the start of World War II, the French Army was equipped with a multitude of encryption methods (Ribardeau-Dumas 1976, Bouchaudy 2019).
At the highest level (secretary of war, army and army corps), the B-211 machine reigned supreme.
At the level of the army, the manual diagonal transposition system SD23 [1] (derived from a system that already existed during the 1st World War) served as a replacement and back-up system for the B-211. There was also the superenciphered five-digit RA code.
At the level of the army corps and divisions, a superenciphered four-digit code was used. Version 69 was put into service on March 1, 1939 and replaced code 68. In the small echelons (battalions, regiments), the three-digit FC series code was used.
The SHD archives from the start of the war (1939 until April 1940) never mention the C-36. Conversely, the B-211 or other means of encryption are mentioned several times.
It is certain that the French Army at this time was equipped with the C-36. There was arguably not enough of them for operational use, and the existing ones were in reserve for later deployment.
Footnote:
[1] This system is also called System 1923 D; D for diagonal and 1923 because
it was published in 1923. SD meaning “Sans Dictionaire” (Without Dictionary),
i.e., it is a manual process that only requires paper and pencil.
4.2.2 The French campaign – The C-36 is used in theaters of war
Shortly before the Battle of France, the C-36 was put into service. A document from March 1940 specifies this upcoming entry into service (SHD-32N431 1940):
IIIrd Army - Staff - 2e Bureau [1] - SECRET - QG [2], March 1940.
Memorandum
I - By DM n ° 8.15.802 - CH/EMA dated March 13, 1940, the ministry
has decided to put into service:
1) The C-36 type cipher machine (temporarily in the EM of CA, DI,
ID, and AD) [3].
2) The JD series code for small unit use, which will replace the FC
series code currently in service.
II - The delivery of these machines and codes to the various large
army units occupying a sector will be made directly to the
headquarters of each army corps by the Bureau du Chiffre of the
IIIrd Army.
III - With regard to the large units in reserve of GQG [4] of army
corps or army, the distribution will take place, because of their
dispersion, at the Bureau du Chiffre of the IIIrd Army on Saturday
March 30, 1940; the addressees of the present note will be good
enough to take all necessary measures to send their cipher officer
or his replacement on the day indicated to take delivery of the
material in question. It is indicated that the weight of the
material to be transported does not exceed 20 kg [5].
Army General CONDE, commanding the 3rd Army, PO [6] the Chief of
Staff.
Addressees: The General Cdt[7] the 21e CA, the General Cdt the
6e ID, the General Cdt the 42e ID, the General Cdt the 6e DIC [8],
the General Cdt the 20e ID.
Another document dated April 1 specifies that the units that have been
equipped with the C36 and associated documents must wait for an order
from GHQ, which will specify the day from which it must be put into
service (cf. 4.3.1).
From March, the units are equipped (SHD-GR28N51 1940):
Translation of an encrypted telegram received by Army Group N°3 on
March 8, 1940.
Sender: ANTINEA [9] - For the cipher officer - Normal operation of
the two machines received on March 7.
The commissioning of the C-36 took a long time. For units that were
not in direct contact with the enemy the commissioning occurred
later, for example, in North Africa (SHD-32N329 1940):
May 19, 1930 - 84th Infantry Division. Mr. Lieutenant General
commanding the Tunisian Fronts - General Staff – 2e Bureau.
I have the honor to acknowledge receipt ... of the instruction
relating to the commissioning of the C-36 cipher machines …
Note: Perhaps the consecutive C-36 deliveries and entry into service
were interrupted by the armistice. Perhaps some of the C-36s ordered
by the French Army were neither manufactured nor delivered and
therefore some of the units may not have been equipped with them.
In the air force archives, no document identifies the C-36. Other systems are explicitly mentioned: machine B-211, superenciphered codes AM, J2, codes of condensation and encryption series F ... We can conclude that (until proven otherwise) only the army was provided with the C-36. The navy used (among other encryption systems) the C-37, which was relatively close to the C-36 but used encrypted bigrams.
Unlike the American system, the Bureau du Chiffre is separate from the signal service. The following is the procedure for sending a message [10]:
- Reception by the Bureau du Chiffre of the message from the authority (it is the authority who decides whether or not to encrypt).
- Drafting [11] (use of abbreviations, placement of spaces … ).
- Encryption (an officer changes the internal key but it is a cipher clerk who sets the message key).
- Addition of the date, the number of groups and indicators (by the cipher clerk).
- The Chiffre [12] gives the message to the signal section.
Footnotes:
- [1] The Second Bureau of the General Staff was France's external military intelligence agency. The Bureau du Chiffre depends on this 2e Bureau. From the EMA to the Division, each military unit has a Second Bureau.
- [2] QG: “Quartier Général”: Headquarters (HQ).
- [3] Abbreviations: CA: “Corps d’Armée”: army corps, DI: “Division d’Infanterie”: infantry division, ID: “Infanterie Divisionnaire”: divisional infantry, AD: “Artillerie Divisionnaire”: divisional artillery. ID and AD are formations that are part of a division. We point out to the reader that the author has chosen to keep the French acronyms in the English translation of the archives.
- [4] GQG: “Grand Quartier Général”: General Headquarters (GHQ).
- [5] A C-36 weighs almost 2.5 kg, therefor, a 20 kg package contain eight machines.
- [6] PO is the abbreviation of "Pour Ordre" equivalent to PP (Per Procurationem).
- [7] Cdt: “Commandant”: Commandant (Comdt).
- [8] DIC: “Division d’infanterie coloniale”: Colonial Infantry Division.
- [9] The code name ANTINEA corresponds to an army because the name begins with the letter A. This code corresponds to either Army 6 or 8, which made up Army Group 3.
- [10] During the period when the French Army was fighting alongside the Americans (from 1943 to 1945), the latter strongly insisted that the Bureau du Chiffre and signal service merge. Nonetheless, the French Army still retained these two entities except during the Italian Campaign.
- [11] In French, the drafting is called “Démarquage.”
- [12] In French, the Bureau du Chiffre is often referred to as "le Chiffre".
4.2.3. The use of encryption at the end of the campaign
World War II has shown that the use of cipher machines represented real progress. Whenever a choice was possible, machines were always used. Accordingly, at Army Group 3 Headquarters, all (or most) of the messages were encrypted using the B-211.
From the end of May, the French Army finds itself in great difficulty. The Bureau du Chiffre fears the compromise of its high-level encryption methods, that is, the RA code and the B-211 machines [1],[2]. The General Staff even fears that the enemy could send false encrypted messages. The emergency system, the SD23, is then used as a replacement (SHD-GR28N51).
Translation of an encrypted telegram that arrived at Army Group
No.3 on May 21, 1940.
Sender: ANNIBAL [3] - For Bureau du Chiffre:
... Telegrams transmitted by radio to the GQG and presenting a
particular secret will be encrypted in the diagonal 1923 system
with the key "Commandant JOUBERT des OUCHES" and is 26 letters
long, ID register 18 or 92 [4].
... Make telegrams of a maximum of 40 groups. Acknowledge receipt
of this telegram in the agreed system.
As of May 16, Air HQ stops using the B-211. As of June 8, GHQ announces
that the SD23 can be used if there is any doubt about the keys to the
B-211. From June 9, the Seventh Army requested that they communicate
only with the SD23. From June 15, Army Group 4 clarified that its
machines were unusable (probably destroyed) and only accepted messages
encrypted in SD23 [5].
From May 15, 1940, RA code was only used on wired links and from May 21 it was withdrawn from service; copies of this code were either cremated or returned to the EMA. It was not subsequently used. The B-211 will be profoundly modified (cf. 5.2).
Footnotes:
- [1] Concretely, the Bureau du Chiffre fears the capture of the machine with the key of the day or worse the capture of the keys as well as the RA code and its superenciphered keys.
- [2] In the case of machine use, messages from the archives contain the print tapes on the back. Without context, it is the B-211 that is used. In particular, numbers are present and the shape of the characters is that of this machine.
- [3] ANNIBAL corresponds to General Georges, Commander-in-Chief of the North-Eastern front.
- [4] The messages encrypted by SD23 were preceded by a numeric indicator containing the register ID identifying the key.
- [5] The procedures for using the SD23 are complex, due to the limitation of the size of a message in this system, messages often have to be divided into several parts. Because of these divisions and the fact that the encryption is manual, the encryption times are extended.
4.3 Use of the machine
4.3.1 Equipment – Equipment provided and number of machines
A document dated April 1 specifies the endowments in the ciphering machines for one of the divisions of the 3rd Army (SHD-32N431 1940). The utensils that comprise a C-36 are specified as well as the documents provided such as instructions for use and keying. We also learn that the C-36 is the normal means of encryption in the dialog between a division and its components (divisional units).
IIIrd Army - 2e Bureau - EM ... - Bureau du Chiffre - N°xxx [1]
- PC [2], April 1, 1940
General Chaulard provisionally commanding the 6th DIC to Mr.
Colonel Commander IDC/6.
SENDING SLIP
- The cipher machine type C-36 N ° 5634 to 35 ... 2 (copies).
Each machine includes two n ° 601-1 mechanically cut keys, an
ink pads can, an oil can, a pair of tweezers and two spare paper
rolls (in addition to the roller in place).
- A carrying strap .... 2 (copies).
- The instructions for the use of the machine [3] - N° 13311 CH/EMA
of January 19, 1937 ... 2 (copies).
- Secret notice N ° 5. 15169 CH/EMA of February 21, 1940 concerning
the internal secret elements of the machine, the message key and
message drafting, copy N° 159 ... 1 (copy).
- Instruction N ° 15470 CH / EMA of February 21, 1940 relating to
the commissioning of C-36 cipher machines. Copy N° 159 ... 1 (copy).
The date of commissioning the type C-36 cipher machine will be
indicated later, as well as the positions to be given to the internal
secret elements of the machine. The C-36 machine will be the normal
process of encryption for the IDC/6 with the DIC and ADC. Code 69 and
the 1923 D transposition system should be considered back-up procedures.
For its relations with the divisional engineering and infantry
regiments and artillery, which so far have no cipher machine, the IDC
will continue to use Code 69 as the normal encryption method.
The attention of the officer in charge of the Bureau du Chiffre and
his replacement will be particularly drawn to instruction n ° 15470
CH/ ... on Chapter III of this instruction (retention of secrecy).
Note: we can see that, unlike the M-209, the C-36 does not have a
carrying bag.
One of the documents specifies that the C-36 number encryption technique is described in a separate manual: Note 32344 CH/FP dated April 29 (SHD-32N431 1940). One would have thought that the encryption of numbers would simply be included in the instructions for use.
The following document corresponds to an inventory of C-36s in a division in June 1940 (SHD-32N431 1940):
IInd Army - 2e Bureau - ... SECRET - PC, June 1, 1940 ...
INVENTORY OF CIPHER MACHINES (Type C-36)
Number Holders
N° 5-632 EM - DIC
N° 5-633 d°
N° 5-634 IDC/6 (EM)
N° 5-635 d°
N° 5-636 ADC/6 (EM)
N° 5-637 d°
All machines including 2 n ° 601 mechanically cut keys, 1 ink pad can,
1 oil can, 1 pair of tweezers, and 2 spare paper tapes are in perfect
working order.
Major General CARLES commanding the 6° DIC PO the Chief of Staff.
Assuming that this inventory, composed of six machines, is representative of
the equipment of a division, we can estimate the number of C-36s in service
in June 1940 when the French Army had 100 divisions {4]: 6 x 100 = 600 machines.
We must also add several tens or hundreds of machines that were equipping the
higher units (army corps and armies). It is also necessary to add several tens
or hundreds of machines to constitute reserves. Hence, we arrive at a number
close to 1,000 machines.
Footnotes:
- [1] The number is illegible.
- [2] PC: “Poste de commandement”: Command Post (CP).
- [3] The machine's manual could not be found in the SHD archives. If any readers have this document and chose to publish it, I would be extremely happy.
- [4] We recall that 30 machines were planned per division.
4.3.2 Preparation of messages – Drafting
Before encrypting a message, the operator mainly modifies it to shorten it. This operation is called drafting (in French, “démarquage”).
The drafting of a C-36 message is described in a document of which the following is an excerpt (SHD-1P136 1942):
Note on the use of abbreviations for establishing encryption using
the C.36 cipher machine - N ° S 2120 CH / FT - April 15, 1940 -
GQG – 2e Bureau – Bureau du Chiffre ...
Some abbreviations should be known by heart:
BTN Bataillon (Battalion) PRA Praticable (Practicable)
CAV Cavalerie (Cavalry) RAS Rien ŕ signaler (Nothing to signal)
DIR Direction (Direction) RCN Reconnaître (Recognize)
ENI Ennemi (Enemy) REN Renseigner sur (Inquire about)
ESC Escadron (Squadron) RGT Régiment (Regiment)
GAU Gauche (Left) RIV Rivičre (River)
HEU Heure (Hour) ROU Route (Route)
KLM Kilomčtre (Kilometer) SIG Signaler (Report)
MET Mčtre (Meter) SOR Sortie (Output)
MIT Mitrailleuse STA Station (Station)
(Machine gun) TEN Tenir (Resist)
NID Nid de résistance TRL Transversale (Transversal)
(Resistance nest) ULT Ultérieurement (Subsequently)
OFI Officier (Officer) VIL Village (Village)
PAT Patrouille (Patrol)
PEL Peloton (Platoon)
...
It is also advisable to use the usual abbreviations, such as
CIE Compagnie (Company)
OCT Octobre (October)
ST Saint (Saint) ...
Example:
For the day of December 12, the cavalry corps requests a credit
for 10 hours movement on the AMIENS SAINT-JUST-LE-GRAND route.
CORPS CAV DEMANDE POUR 12 DEC CREDIT MOV DIX HEU SUR ITI AMIENS
ST JUST LE GD
CAUTION: "The desire to summarize must not, however lead to a
waste of time nor to composing incomprehensible texts" ...
VII - A good working method will entail the instructions from
the beginning indicating the words and expressions used with
the machine C-36 in red pencil on the condensation notebook ...
The last paragraph refers to the condensation notebook. This document
of approximately one or two pages includes the abbreviations most
frequently used in transmissions
(Tant).
Regardless of this drafting, those who wrote messages used code names to hide the names of units and/or senior officers, among other things. Code names beginning with the letter "A" corresponded to higher units up to army level. Code names beginning with "B" corresponded to the army corps. Code names beginning with "C" corresponded to divisions, and so on.
Here are the unit names of the Northeast Front (SHD-10P386 1945) for the period May 5, 1940:
AURORE GQG, Commander-in-Chief (General Gamelin)
ARLESIENNE GQG reserves: Xth Army (General Altmayer)
ANNIBAL Commander-in-Chief of the North-Eastern Front
(General Georges)
ALOUETTE Army Group n ° 1 (General Billotte)
ANGELUS Ist Army (General Blanchard)
ANGORA IInd Army (General Huntziger)
AMPERE Army Group n ° 2 (General Pretelate)
AQUILON IIIrd Army (General Condé)
ARCHINARD IVth Army (General Requin)
ARCHIDUC Vth Army (General Bourret)
ANDROCLES Army Group n ° 3 (General Besson)
AMILCAR VIth Army (General Touchon)
ARGONAUTE VIIth Army (General Giraud)
ATLAS VIIIth Army (General Garchery)
ARISTOTE IXth Army (General Corap)
4.3.3 Key distribution
The SHD archives contain several key delivery slips. Here is an example (SHD-32N431 1940):
IIIrd Army - General Staff – 2e Bureau - N° 96/2/CH - SECRET - QG,
April 20, 1940.
The General of the Army CONDE, Commander of the IIIrd Army to the
General Commandant the 6° DIC (Staff 2 ° Office – Bureau du chiffre).
SENDING SLIP
1° / Table "A" N ° 97/2 CH dated April 18, 1940, relating to the
internal secret elements of the C-36 cipher machine valid in the area
of the IIIrd Army from April 22, 1940 at midnight …... 3 (copies)
2° / Table "B" N ° 98/2 CH dated April 18, 1940, relating to the
starting key of the C-36 cipher machine valid in the area of the IIIrd
Army from April 22, 1940 at zero hour ...... 3 (copies)
3° / Exercise telegram N ° 99/2 CH dated April 18, 1940 intended to
verify the keying of the cipher machine C-36 ...... 3 (copies)
A duplicate of this slip is to be returned as a matter of urgency to the
Bureau du Chiffre of the IIIrd Army as an acknowledgment of receipt.
Observations: Documents to be distributed to the owners of the C-36
cipher machine. It remains understood that these Tables A and B must
be used exclusively in the area of the IIIrd Army. The unit that holds
them must incinerate them when it passes into the zone of another army
or in the zone dependent on the GQG; in this case, new tables will be
given to it by the large unit to which it will report ...
As we can see, the keys consisted of at least two parts:
- Table A relating to internal secret elements. Clearly, this table represents the configuration of the pins and the letter of the setting from which the variable offset (slide) of the machine is deduced.
- Table B relating to the starting key. Clearly, this table represents the substitution alphabets to encrypt the message key (cf. 4.3.4).
Some slips also mention a Table C, which corresponded to an exercise telegram intended to verify the setting of the key. Other slips do not mention Table C. We can imagine that in this case, it was integrated into Table A. Some slips simply indicate the endowment of an exercise telegram.
By inspecting several key delivery slips, the following was deduced:
Before the war, the various units received a circular describing the use of a special key, the "ZERO" key, which was intended to be used in the event of the mobilization of troops or when receiving a telegram indicating the setting of the key. It seems that several of these circulars had been updated according to the means available. Indeed, the document (SHD-7N4235 1940) "Introduction to the Zero Key" of January 27, 1938 specifies that it replaces the copy of November 13, 1937, and the latter is to be cremated.
The document of January 1938 includes in particular the key setting for large model (B-211) and small model (C.36) machines. The circular specifies that the allocation of small machines (C-36) will begin during 1938 and will continue in the following years.
Note: as noted elsewhere, no document (other than this one) refers to the C-36 before it entered service in April 1940.
In early 1940 (April to June), a C-36 key was valid inside an army and allowed dialog between its staff and the different army corps and divisions of which it was comprised. It was stipulated that if a division was absorbed by another army, it was to destroy its keys and wait for more keys from its new assignment [1].
The keys were valid from one to several weeks; for example,
- Key 97 of the 3rd Army was valid from April 18 to May 10, 1940, therefore, 22 days (Table A key N ° 97/2CH and Table B key N ° 98/2CH).
- The key n° 2224 of the 2nd Army was valid from May 28, 1940 to June 4, 1940, therefore, seven days.
- The key n° 2734 of the 2nd Army was valid from June 5 to June 11, hence, six days.
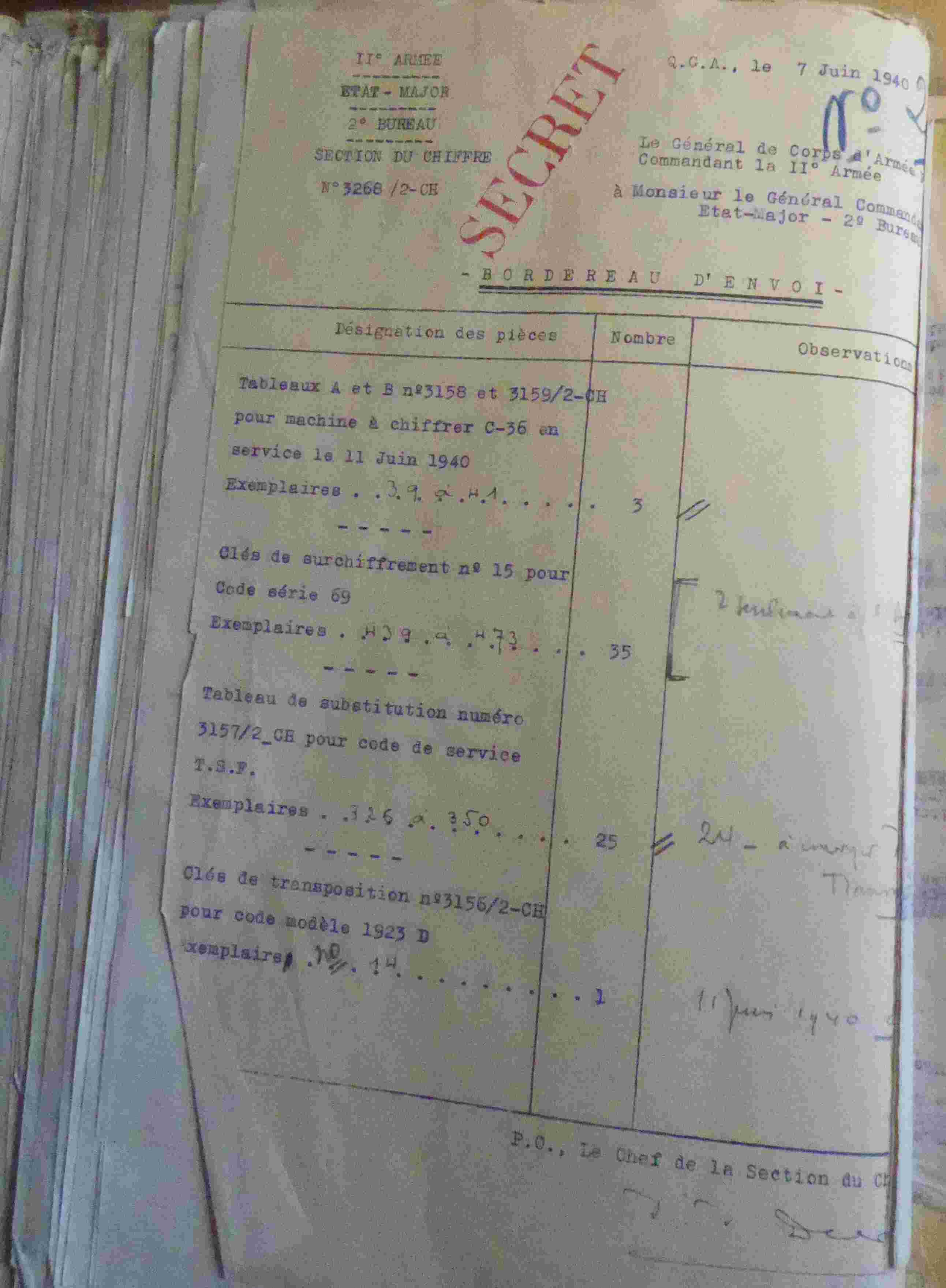
The slips encountered in the archives normally only concerned the keys for the C-36 (Tables A and B) intended for a division. Figure 1 (SHD-32N431 1940) shows another type of slip that corresponds to the set of keys used to communicate between the army's EM and its divisions: the C-36 keys but also the superencipherment keys of code 69, the 1923 D transposition keys, and even the substitution tables for the radio service codes. It can be deduced that there were at least three C-36s for each army EM.
At the end of the campaign in France, the army crumbled and the security breaches resulting, in particular, from the supposed capture of machines and documents from the Bureau du Chiffre concerned the authorities, and the security measures were consequently reinforced (SHD-GR28N51):
Translation of an encrypted telegram that arrived at Army Group No.3
on May 23, 1940.
Sender: ANNIBAL - For the Bureau du Chiffre:
1) Needed to strengthen the security of the encryption in C.36.
2) Arrange for daily change of the “calage” letter [2],[3].
3) Send the list of “calage” letters under the same conditions as the
sending of keys ... Telegram forwarded to ARGONAUTE AND AMILCAR [4] …
Footnotes:
- [1] This was the case, for example, for the 6th DIC (Colonial Infantry Division), which belonged to the 3rd Army and which was incorporated from May 14, 1940 into the 2nd Army who were in difficulties in the Ardennes following the German breakthrough.
- [2] The definition of the “calage” letter is provided in paragraph 6.3.5.4. In short, this letter determines the slide.
- [3] If a daily change in the “calage” letter is recommended, we can deduce that this was not the case previously. Perhaps the validity of a registration matched the validity period of the rest of the key, i.e., the configuration of the PINS.
- [4] ANNIBAL corresponds to the Commander-in-Chief of the North-Eastern Front, that is, General Georges. ARGONAUTE corresponds to the 7th Army and AMILCAR to the 6th Army (cf. 4.3.2).
| Fig 1: Shipping slip for key tables A and B |
4.3.4 Indicator method
In one of the ARCSI bulletins (ARCSI 1978), an extremely interesting document dated May 7, 1940 was uncovered. It was a letter from a cipher officer (his name does not appear) criticizing the indicator method used in 1940 for cipher machines. To conclude, the officer proposed a new method. However, in his review, he almost completely described the current method. Let us give the floor to this officer:
... You have received my suggestions in such a welcoming manner that I
take the liberty of submitting another to you. It concerns substitution
alphabets for machines. Currently, the columns are the same for the
alphabets of the B 211 and C 36. Only the column headings change.
Therefore, the key groups for the two machines correspond, that is, they
give a key possible for use with both machines (these two keys are also
different from each other).
Now, in fact, it happens that the armies, sending a telegram circular to
the CA and DI who are dependent on them, use the C 36 machine for this
purpose. The CA cipher clerk receiving this telegram is therefore obliged
to
1°/ take out the large machine documents
2°/ take out its key
3°/ put it on the machine
4°/ try a few groups
Then, faced with a failure, repeat the same process with the small
machine, thus, representing a waste of time, which seems unnecessary and
can easily be avoided.
What were we looking for by endowing the two systems with similar
characteristics? To furnish the telegrams deriving from the two machines
with an identical appearance. But there is a danger. Due to the
multiplicity of telegrams and commissioning the small machine FOR ALL
armies, in the key groups, a letter from the first key group will have
three possible letters corresponding to the second group, which will
always be the same. Hence, if an enemy cryptanalyst is unable to
comprehend the letters chosen by the operator, he can, at least,
- Recognize the location of the two key groups,
- Reconstitute the replacement alphabets for all armies ...
From this letter, we can deduce a number of things. First, a B-211 or C-36 key is valid for a single army. Second, that only the CAs are equipped with B-211s but not the divisions. Third, that the C-36 equip the EM of armies, CAs, and divisions. We can also deduce that the indicator is made up of two groups (10 letters). The message key derives from a base group, which is a group of five letters that is encrypted the first time with a first substitution alphabet, which gives the first indicator group. The second group is only used for checking; it is the same group encrypted with a second substitution alphabet. As the base group is composed of only five letters, it corresponds directly to a C-36 message key but not to a B-211 key, whose key must indicate the position of the four wheels and the two half-rotors, that is, six letters unless one identical letter configures several wheels or half-rotor. The officer's description tells us that the situation is actually worse: Each letter of the group from which we deduce the key is associated with three letters in the substitution alphabet. Consequently, there are only 10 possible letters (26 ~ 3 x 10) for each letter of the key group. This greatly reduces the key space. For example, for the C-36 we can imagine that for a key table we have ABCDEKLMNO as the column head (i.e., the letters of the key group). A message key should only use these letters, for example, NDKLE.
Fortunately, in the archives of the SHD, an unexpected discovery occurred: A complete set of keys for the B-211 dated October 25, 1941, which included an example of packaging (SHD-1P136 1942). This example of a key made it possible to confirm the preceding deductions: There was indeed a basic group of five letters, which was encrypted twice by using a first substitution alphabet for the first indicator group and a second substitution alphabet for the second indicator group. The letters of the substitution alphabets were distributed in 10 columns of two or three letters. The letters ABCDEFGHIK (for the B-211) acted as column heads. The first and last letters of the base group corresponded to the (inverted) position of the two half-rotors. Finally, the last four letters of the basic group corresponded to the position of the four key wheels. Thus, the first letter has two uses: to position a key wheel and the second half-rotor. Remember that the position of the key wheels, which have between 17 and 23 sectors, is marked with a letter between A and Y (J and W being omitted) [1]. In conclusion, not all the possible message keys can be chosen. We also learned that the two indicator groups were the first two groups of the cryptogram.
These documents make it possible to completely reconstitute the indicator method used until June 1940, however, they did not state whether this method still applied to the C-36 after this period. Table 3 presents an example reconstructed from the authentic key table from October 1941.
For a message encrypted in B-211, suppose the message key is HDBACH (position of the half-rotors: HD; position of the four key wheels: BACH), the base group becomes DBACH, which is encrypted with the two substitute alphabets, and we obtain, for example, the following indicator: GAUOK JZAGR (or NFVBJ HUNCL … ). These two groups are added at the beginning of the cryptogram.
The letter from the young officer of May 1940 specifies that the column heads are different in the case of the C-36. Suppose the heads are ABCDEKLMNO for the C-36 for a specific key table. The NDKLE message key becomes (with the same alphabets) SGZLQ MHTEX (or XNHIM ZJDKP … ). As in the case of the B-211, this method of masking the message key does not allow the use of any key for the C-36 because there are only 10 column heads. In the preceding example, the key FPQGQ cannot be used.
Table 3: Example of two substitution alphabets used with the 1940 indicator system
-------------------------------
: A: B: C: D: E: F: G: H: I: K: column heads B-211
: -: -: -: -: -: -: -: -: -: -:
: A: B: C: D: E: K: L: M: N: O: column heads C-36
: -: -: -: -: -: -: -: -: -: -
: U: A: O: G: Q: C: L: K: R: W:
: V: F: B: N: D: H: I: J: S: T: 1st substitution alphabet
: : P: : E: M: Z: : Y: X: :
: -: -: -: -: -: -: -: -: -: -:
: A: Z: G: J: X: T: E: R: P: Q:
: N: U: C: H: P: D: K: L: M: O: 2nd substitution alphabet
: Y: V: I: : F: S: : W: Z: :
-------------------------------
Footnote:
[1] In fact, the reality is more complex given that the key implied the
position of four rotors because it entailed a modified B-211.
4.3.5 Other procedures
Frequently, there are memos about security. For example, the note of May 15, 1940 from the Bureau du Chiffre of the 6th DIC (SHD-32N431 1940):
May 15, 1940 - Security note - ... In particular with regard to C36
machines, information concerning the packaging, and a fortiori,
relating to the making of the keys, should never be placed in the
cover of the devices.
Another document (SHD-GR28N51 1940) reminds the cipher clerk never to part with their C.36:
Army Group N ° 3 - General Staff – 2e Bureau – Bureau du Chiffre
- Translation of a ciphered telegram received at GR/3 on May 28, 1940
at 4:40 p.m. - Sender: ARCOLE ...
For the cipher officer: Subject: Security. It was reported that in
some large units C.36 machines had been lost as a result of devices
being left during transport in baggage vans. This way of doing things
is absolutely to be avoided. C.36 machines are fitted with straps
allowing users to carry them on the shoulder strap. In any case,
their owners must not part with them. Telegram sent to interested
Army and Army Groups.
A document dating from May 1940 informs us how the repair of the machines was
planned (SHD-32N329 1940) [1]:
C.36 Cryptographs will be repaired:
- In the first degree through the care of their holders.
- In the second degree by the care of General Cdt of the Tunisian Fronts.
Subsequent instructions will fix the authorized first degree repairs.
In order to constitute a repair workshop in the first degree, the
commanders of large units as owners of the C.36 machines to whom this
note is addressed will each designate a qualified non-commissioned
officer or master corporal, radio precision mechanic, or watchmaker
preferably. The officers in question will be instructed during an
internship at the secondary level workshop …
Footnote:
[1] The manual for the C-36 has not been found. In the manual of the C-36M2
(which is probably extremely close, cf. 7.3),
the only operations authorized for the holders is the replacement of the
paper and the ink pad as well as the oiling of the machine.
4.3.6 A sample message (one plain text)
A typed message (SHD-GR28N51 1940) dated late May 1940 certainly contained a message encrypted in C-36. Indeed, the decryption tape was glued to the back of the message and contained numbers coded in letters.
Message N° 238/I. Sender: ARLESIENNE. Addressee: Army group n° 3,
1st Bureau. May 31, 1940, 3.35 p.m.
Repetition of telegram no.30-21. Losses of May 29: Officers: 3,
Men: 146. Information concerning only CANADIANS, DAPHNIS, DAVOUST,
and FALCONNET.
Tape coming from the machine glued on the back:
REPEAT k DU k WQH k JO k PER k WFW k MAI k OFI k WE kk HOM k WGRN k
REN k CONCERNING k ONLY k CANADIAN k DAPHNISLDAVOUT k FALCONET k NO
k WPQZ k SUR WO k
Remarks:
- The letter "k" was used to highlight spaces.
- The code name ARLESIENNE corresponds (cf. previous paragraphs) to the 10th Army.
- The code names CANADIAN, DAPHNIS, DAVOUT, and FALCONET correspond respectively to the 13th Metropolitan Infantry Division, the 5th Colonial Division, the 7th Colonial Division, and the 2nd Light Cavalry Division (DLC).
- The numbers are easily decipherable if we accept a slide of 23: WQH JO = 30 21, WFW = 83, WE = 8, WGRN = 740, WPQZ on WO = 236/1
- The shape of the characters corresponds to the C-36.
4.3.7 The point of view of a member of the French Cipher Office
This article describes the C-36 and its history and therefore obviously cannot be particularly emotional. But we must not forget that this machine was used in a time of war by men who lived through dramatic moments, some of whom died while undertaking their service. Here are some extracts from the diary of Captain Raoul A. Lemennicier, which recount his memories of war in particular the German breakthrough of May 1940. At that time, he was the head of the Bureau du Chiffre of the 9th Army under the orders of General Corap who endured the full force of the German attack in the Ardennes (Link):
(October 1939)
… Life is monotonous, work is no less. This period of war is little
different from the time of peace. Office hours do not change.
Fortunately, my duties require me to carry out inspections in the
large units of the army. The repair of the cipher machines obliges
me to undertake a few trips to La Ferté sous Jouarre where my boss
is located, the Commander Joubert des Ouches (GQG).
(May 10, 1940)
The quiet period ended on May 10 on the first morning. Nothing
foreshadowed the German attack …
(May 15)
There is no longer any question of transporting the EM of the 9th
Army in Chimay in Belgium as the order of operations had planned.
In the Bureau du Chiffre the work became overwhelming. Two
officers are on duty day and night. It is hardly possible to sleep.
Meals are eaten quickly …
(May 16) The Germans are in Marles, 15 km west of our PC. In the
corridors there is talk of resisting on the spot. The 9th Army has
passed since the day before under the orders of General Giraud.
All the office managers have destroyed the secret archives. I
decided to do the same. All the papers are burned, including
documents in reserve. We are fortunate to have a central heating
boiler nearby, which allows us to incinerate 200 kg of paper in
a short time. The cipher machines are prepared for destruction as
soon as the defense of the exits of Vervins kicks in ... Without
even having time to prepare luggage, we are ordered to leave
immediately, charged with strictly essential equipment (B-211 and
C-36 cipher machines, codes, and suitcases) ... At around 4 p.m.,
we learned that the headquarters of our army was going to move to
Bohain ... We had barely identified our room (the girls' school)
when the messages to be encrypted and decrypted arrived ... Later
I learned that the Germans were already in Guise. So we had
crossed their ranks without knowing it. What luck.
(May 17)
The officers are summoned by the head of the First Bureau, Cdt
Rousselet (killed in action that same day). He takes a dozen of
them with him, including Velut and Lauzanne. Under his orders,
they must ensure the defense of the Wassigny agglomeration where
General Giraud and his advanced echelon have withdrawn. The
Colonel makes a short speech from which it appears that the
situation is hopeless ... Before joining my post, I take care to
destroy all the cipher material. With a hammer and a rifle butt,
I demolished the B-211s and the C-36 [1]… In the evening, I received
a report from Captain Velut in Wassigny. Everything is fine, he
told me. With Lauzanne, he continues to encrypt and decrypt
messages. They only have one system left without a code, which is
also satisfactory [2]. We exchange keys, which will allow us an
encrypted correspondence. The night is calm. In the shelter near
my PC I can take a few hours of rest.
(May 18)
At daylight, I received word from Captain Houssay. I have to join
the headquarters at 7 am and go to the GQG at La Ferté sous Jouarre
to collect new documents from the Bureau du Chiffre. But long
before, I was summoned by the Deputy Chief of Staff to decipher
messages (machine) received during the night. Decryption is
impossible as the material is destroyed ... As soon as I got back
to QG, an encrypted message was handed to me. I deciphered it
easily. The QG of the 9th Army must immediately move to Catelet
20 km west of Bohain ... A quick glance at the door to the street
and I see one of our machine gun cars on fire. The one closest to
us continues to fire, but its firing is less intense. A wounded man
who dies immediately is transported to the porch of the cafe ...
Around 6 p.m. the firing suddenly ceased and heavy footsteps were
heard nearby. What's going on? We will soon know. As I walked to
the exit with Lt Pochtovick onto the street, I found myself face
to face with a German soldier, armed to the teeth, presenting me
with the barrel of a machine gun ... I went out into the street
where I joined a group of officers who, like me, had just been
"taken prisoner."
Footnotes:
- [1] In French: “je démolis les B.211 et la C 36.”: there were therefore at least two B-211s and only one C-36.
- [2] The only encryption system they have left is probably the SD 23 diagonal system.
4.4 German cryptanalysis
Several TICOM documents point to the failure of the German cryptanalysts. A priori no message encrypted by the C-36 was decrypted by them during this period. Several elements explain this failure. First, the late entry of the machine into service. Then, the almost exclusive use of wire telegraphy in the period preceding the German breakthrough. Finally, the brevity of the campaign starting in May 1940: German cryptanalysts did not have time to develop methods for attacks following the capture of machines or secret documents.
The TICOM documents tell us that the Germans discovered the functioning of the C-36 and the B-211 following captures made during the campaign of May 1940 (TICOM I-78 1945, TICOM I-128 1945).
Footnote:
[1] TICOM (Target Intelligence Committee) was a secret Allied project formed in
World War II to find and seize German intelligence assets, particularly in the
field of cryptology and signals intelligence.
References
- ARCSI, 1978. Le 7 mai 1940 (Systčme indicateur du B-211 et C-36 [anonyme]). Bulletin de l’ARCSI n°6.
- Bouchaudy, J-F, 2019. Genuine French WWII M-209 cryptograms, Cryptologia, 43:5, 359-371, DOI: 10.1080/01611194.2019.1596180
- Ribadeau-Dumas, L. 1976. Essai d’historique du chiffre de l’armée de terre, 5ičme partie: la guerre 1939-1945, Bulletin de l’ARCSI, Nouvelle série N°4, p33–52
- SHD – 7 N 4235. 1940. EMA (Etat-major de l'armée) – Section du Chiffre – 1) Organisation du service du chiffre et du service cryptographique aux armées (1919-1939). 2) Chiffrement: étude, plans de chiffrement, machines ŕ chiffrer, surveillance de la correspondance chiffrée (1921-1939). 3) Télégrammes reçus (1921-1940).
- SHD – 32 N 329 – 1940. 84° D.I.A. 2e bureau – correspondance expédiée et reçue relative au chiffre (sept 90 – mai 1940)
- SHD – 32 N 431 – 1940. Correspondance expédiée et reçue de la section du chiffre (septembre 1939 - mai 1940)
- SHD - 1 P 136. 1942. Délégation générale du gouvernement en Afrique française – 1941-1942
- SHD – 10 P 386. 1945. 4ičme Bureau. Collection des télégrammes expédiés et reçus. Novembre 1944-Mai 1945
- SHD – GR 28 N51. 1940. Groupe d’armée N°3, Etat-Major, 2e Bureau. 1939-1940.
Web Links
- Lemennicier, B., 1996. Site Web de Bertrand Lemennicier. In memoriam, OFLAG XB, Nienburg, Germany, 1940-1945. (link).
- Tant, D, 2021. Le répertoire de condensation. ARCSI. (link).
- TICOM I-78 – Report on information obtained from PW Obstlt METTIG – 1945. (link).
- TICOM I-128 – Deciphering achievement of In 7/VI and OKW/Chi – oct 1945. (link).